By default the Nerdio Manager for Enterprise is publicly available. I had the question to disable public access and to adhance the security of the entire Nerdio infrastructure. In this blog series I’ll walk you through the steps to do this.
There are several components that we need to harden:
- App service
- SQL
- Keyvault
- Automation account
- Storage account
Because of the number of components, I decided to split it up in multiple parts. In this part I’ll focus on the App Service
The Nerdio App Service is by default publicly available if you have the url. You still need access of course to use it. We want to make sure that it’s only reachable from either a specific IP address/range or Virtual Network. In this part I’ll walk you through the steps to take to secure the App Service.
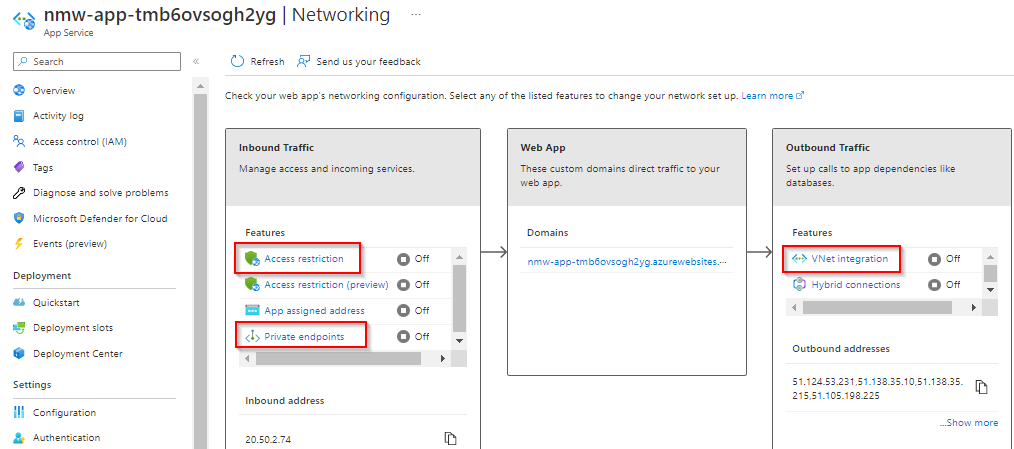
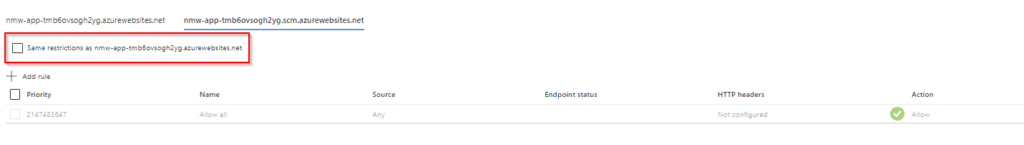
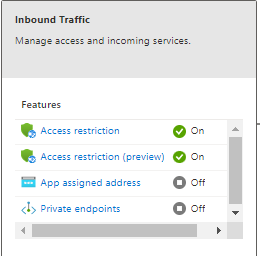
In the screenshot below you can see the Access restrictions in the Networking blade and the status of it.
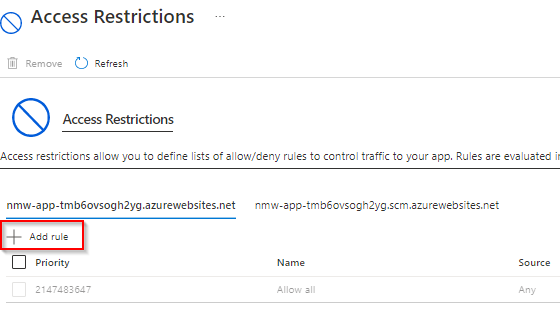
When selecting Access Restrictions you can add a rule. Notice that there is a Allow All rule in there by default. Click Add rule to get vertical extra menu on the right.
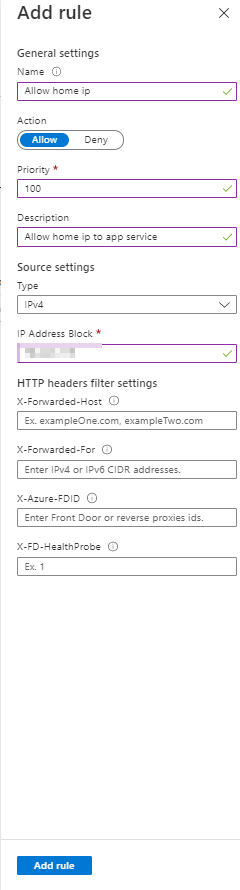
Here you can specify the name of the rule, the priority, the Action and the IP address block.
You can do this for both azurewebsites listed. Also very important it that when you add a rule the default rule will go in deny state.
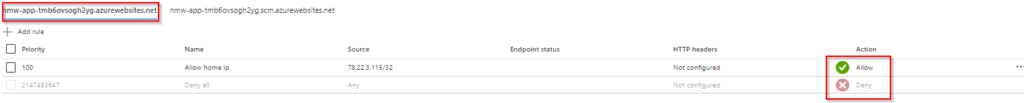
When done you will see the status changing.
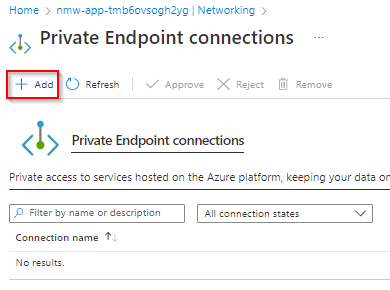
Rather than allowing IP addresses, you can specify from what subnet you can reach the App Service by using a private endpoint.
Click on Private Endpoints and Add.
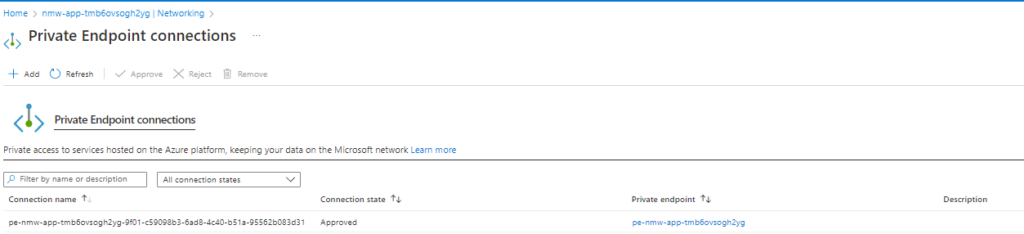
Next, select the Virtual Network and subnet and choose you want to integrate it with an Azure Private DNS zone.

When the deploying succeeded you will see the private endpoint in Approved state.
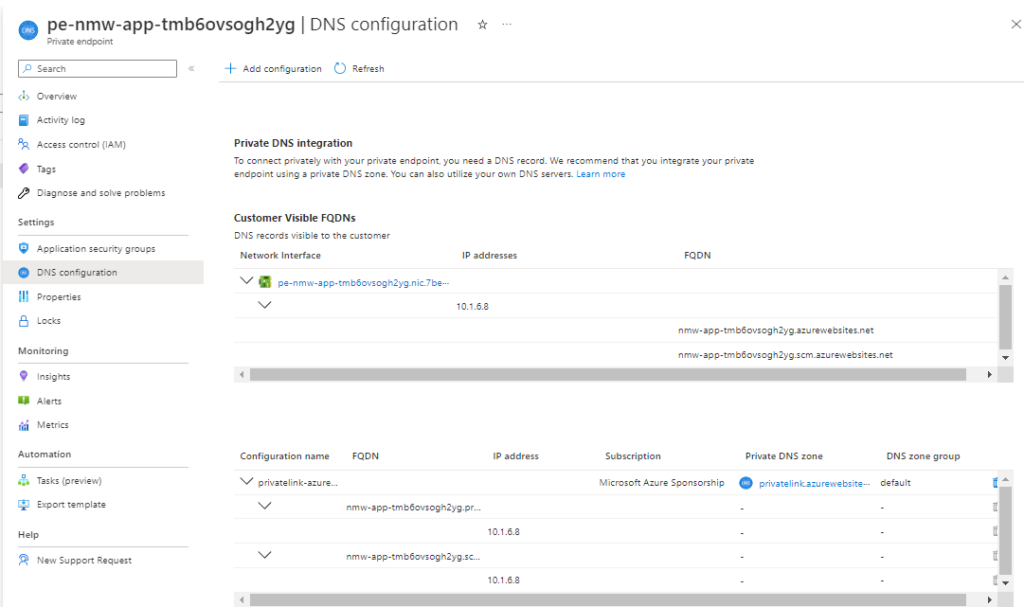
When I go to Private Link Center and check I can see the private endpoint and the DNS config it has.
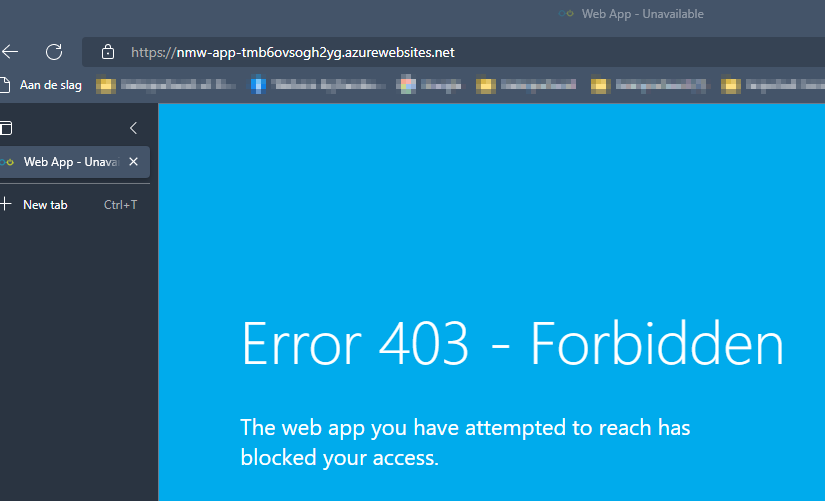
When I can check the App Service now from my own pc I can see that I can’t access the App Service anymore.
This concludes this first part in this series, stay tuned for part 2. If you have any questions about this part, feel free to contact me.
2 thoughts on “Harden Nerdio Manager for Enterprise Part 1 – App Service”